In The State of Ransomware 2020 report, over half the participating companies surveyed across 26 countries reported that they had been hit by ransomware in the past 12 months. This result demonstrates the critical need for predictive zero-day threat identification and protection as advanced threats like ransomware become more targeted and evasive.
In this fourth in our series of articles on making the most of the great new features in XG Firewall v18, we’re going to specifically focus on the new capabilities in XG Firewall v18 designed to protect against the latest zero-day threats such as new ransomware variants.
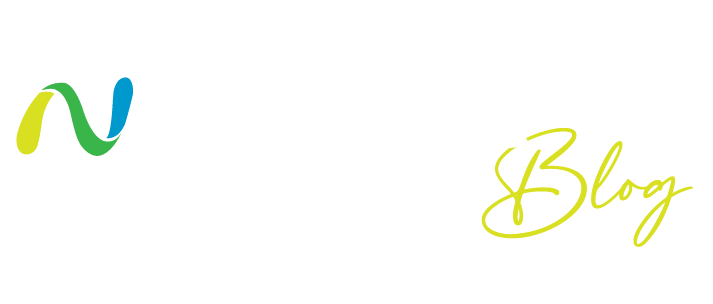
Xstream Threat Protection
In previous articles, we covered the Xstream architecture and the new DPI engine, the new TLS inspection solution, and the Network Flow FastPath. These all play a critical role in identifying and stopping the latest zero-day threats. This article highlights the new cloud-based Threat Intelligence and Sandstorm sandboxing technologies which are part of the Sandstorm Protection subscription.
How it works:
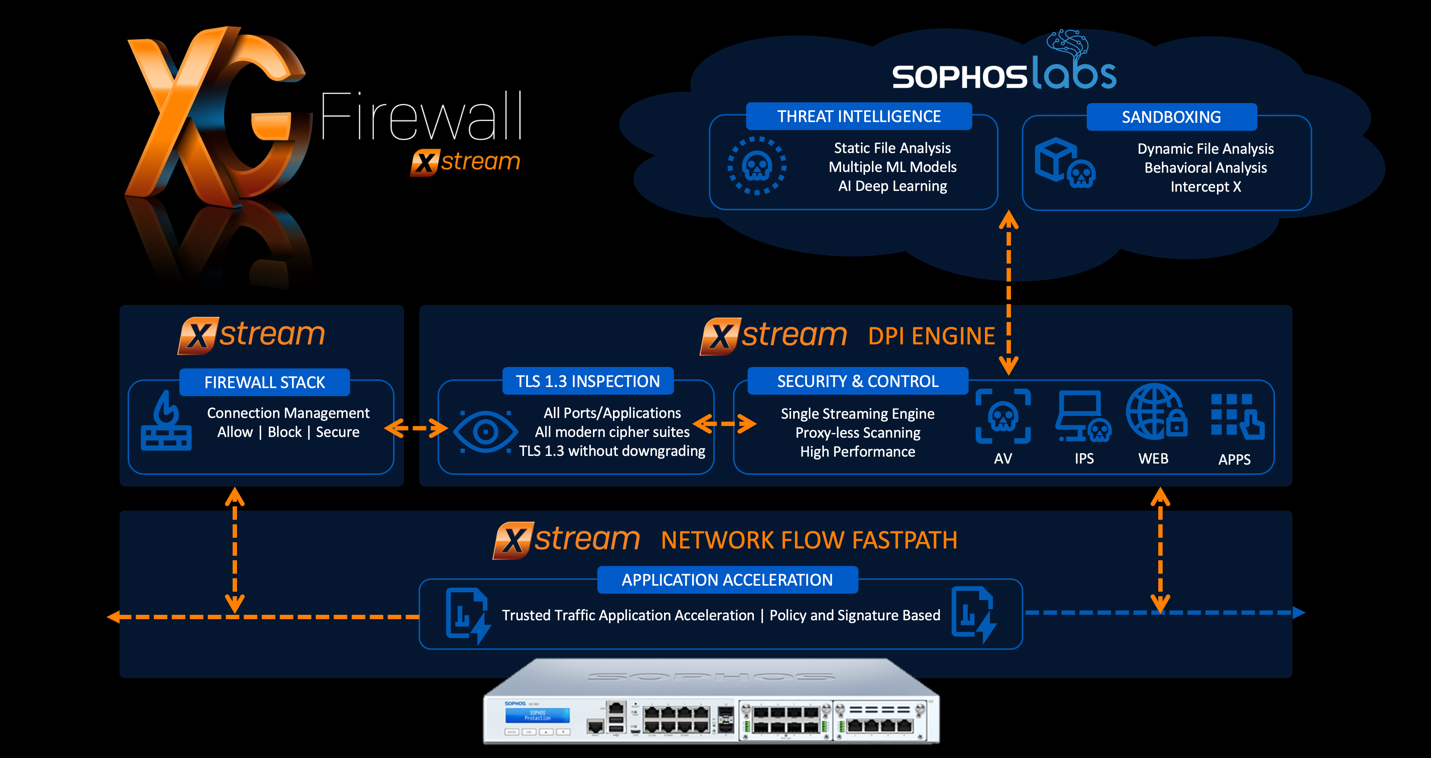
XG Firewall v18 includes new machine learning (ML) based threat intelligence and a newly enhanced version of Sandstorm sandboxing, which work together to identify the latest zero-day threats. Both are powered by SophosLabs Intelix, which uses machine learning technology, decades of threat research, and petabytes of intelligence to provide unmatched protection against new and previously unseen threats.
When XG Firewall’s Xstream DPI engine performs AV analysis on a file entering the network and determines there is active code, it holds the file temporarily and sends it to the SophosLabs Intelix service in the cloud for both static and dynamic (sandbox) analysis. It then provides a detailed overview of the results and only releases the file to the downloader or email recipient if the file is declared safe.
This last step is important, as many advanced malware solutions on firewalls release a file to the end-user before the analysis is complete, potentially resulting in an extensive and expensive cleanup if the file is then ultimately convicted as a threat once all analysis is finished.
Let’s take a look at what happens to a file that is scanned in a bit more detail:
Threat intelligence analysis:
Threat intelligence uses multiple machine learning models to analyze the characteristics, features, genetics, and global reputation of the file. It compares the new file with millions of known good and bad files in the SophosLabs database to render a verdict in seconds without the need to execute it in real time. This makes it remarkably fast and effective at identifying new threats and new variants of existing threats, particularly with files which are not easily sandboxed, such as password-protected documents.
Sandstorm sandboxing analysis:
At the same time a file is submitted for threat intelligence analysis, it is also submitted for dynamic behavioral analysis in our cloud sandbox environment. Because it’s cloud-based, there’s no additional software or hardware required, and no impact on firewall performance.
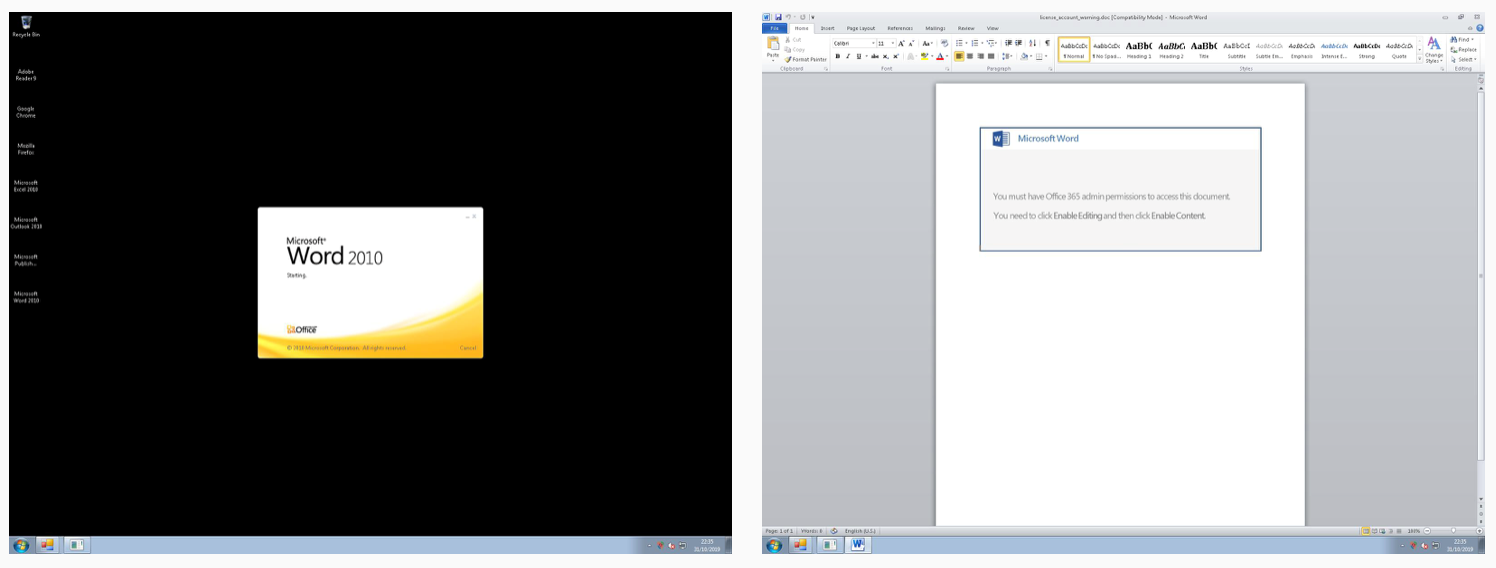
To identify threats based on their behavior, SophosLabs has integrated the latest protection technologies from our industry-leading Intercept X next-gen endpoint product into the Sophos Sandstorm sandbox. This includes deep learning analysis, exploit detection, and CryptoGuard to detect active ransomware encrypting files in real time. The sandbox also monitors all file, memory, registry, and network activity as well as sandbox evasion techniques. No other firewall can offer this kind of run-time analysis with the world’s best threat protection, Intercept X. And no other firewall offers the level of insight and reporting that XG Firewall provides – including a time-lapse series of screen shots showing events during the file execution.
Sandboxing is particularly effective at detecting threats that can lurk in normally benign files that may not have any obvious malicious characteristics. Office files with macros or benign executables and application updates that have been subverted by hackers are prime candidates for detection through sandboxing.
How to make the most of Xstream Threat Protection
There are three key things you need to enable this critically important protection:
- Ensure your XG Firewall license includes the Web Protection and Sandstorm Protection subscriptions. You need both of these subscriptions active to be protected from the latest threats. The new threat intelligence analysis in XG Firewall v18 is part of the Sandstorm license, adding tremendous value over the previous version at no extra cost. Log into your XG Firewall and go to the Administration menu to see a list of your active subscriptions. Be sure to contact your preferred Sophos Partner immediately if you don’t have both these protection subscriptions active.
- The new threat protection technology in XG Firewall can only inspect and analyze decrypted traffic, so ensure that you’re inspecting TLS-encrypted web traffic. With the vast majority of web traffic now encrypted, it’s critical that you decrypt and inspect files being downloaded onto your network to have them analyzed for potential threats. Check our recent article on the high-performance TLS inspection solution in XG Firewall v18 for full details on how to take advantage of this great new capability.
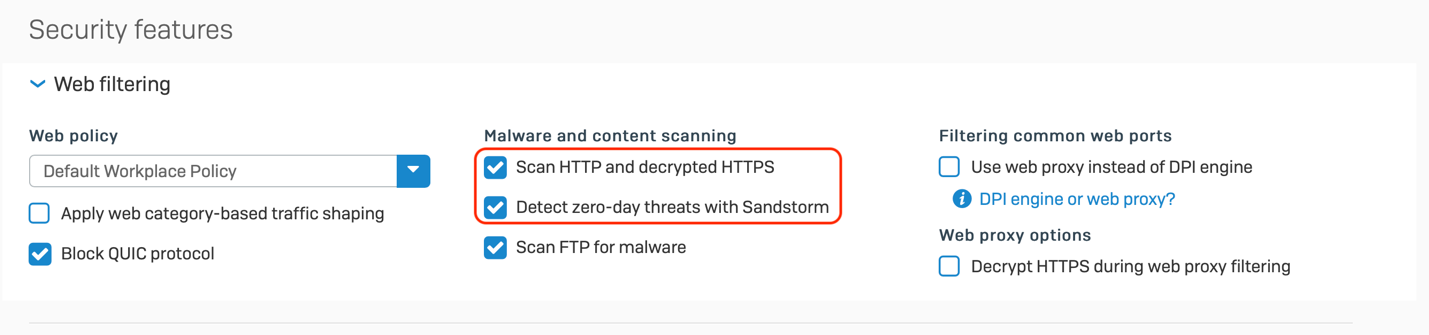
- In all firewall rules governing web traffic for your network, ensure you have the following two web filtering security options set to scan web traffic and use the latest zero-day protection technologies outlined here:
That’s it – it’s really that easy!
Check out this video for an in-depth guide on making the most of this new feature, a detailed look at the new and improved threat intelligence reporting, and how to interpret the results:
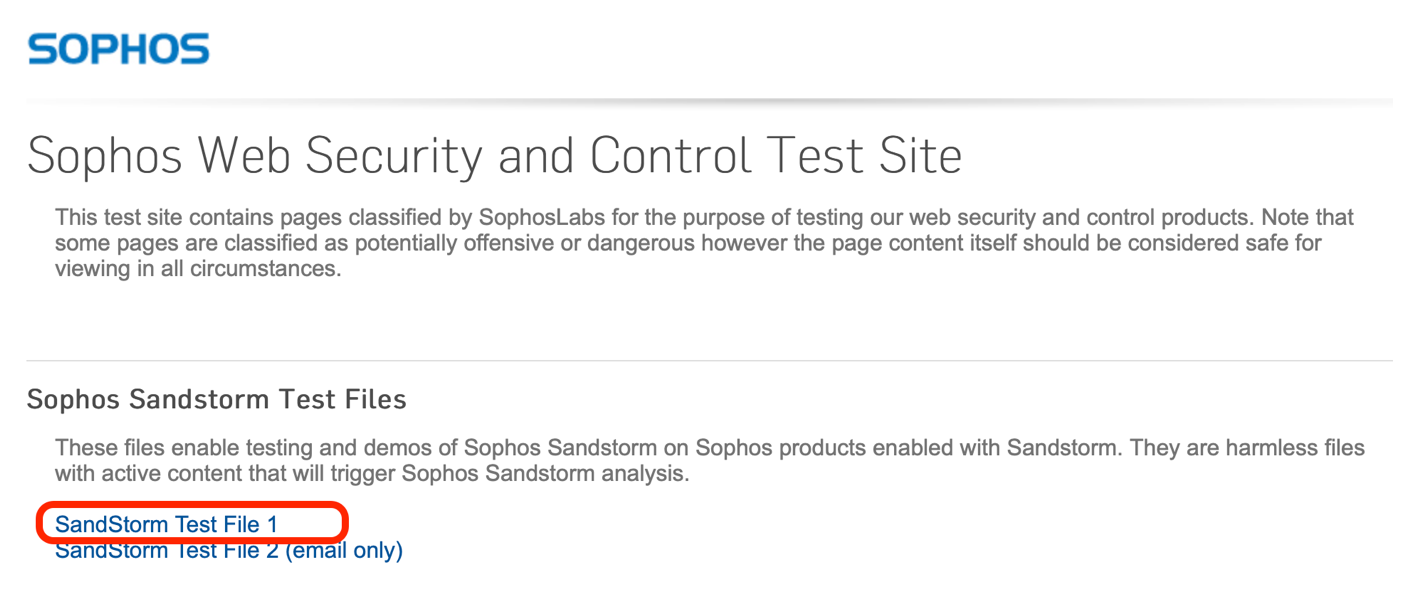
Testing it yourself
There’s a convenient and harmless test file you can find at SophosTest.com, which will provide a sample report for you to review.
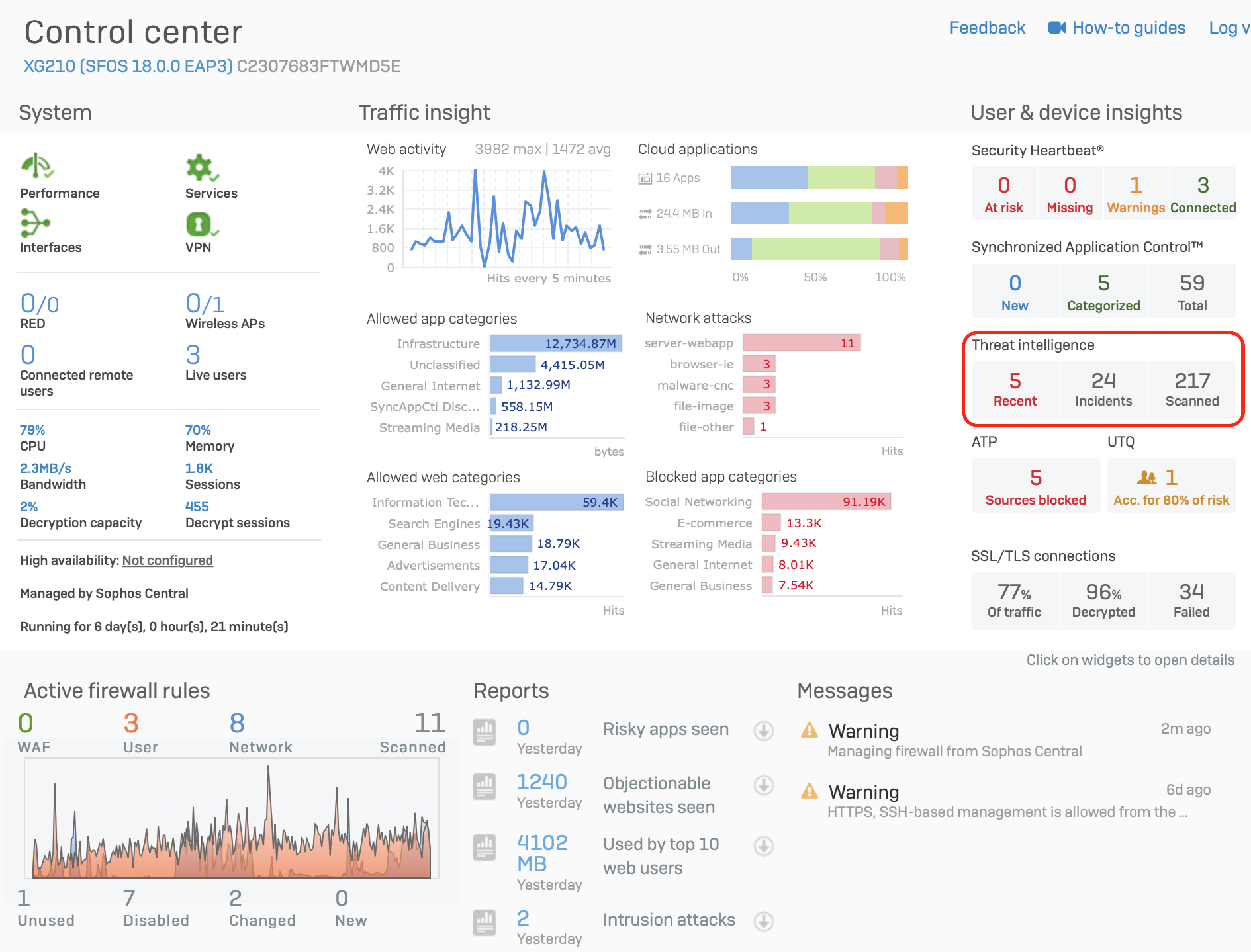
Also, keep an eye on your Control Center widget for any recent file downloads that have been analyzed and then drill down for further details.
When you click the Control Center widget (highlighted above), you can drill down into a detailed list of files analyzed and their results. Mouse over the results column to display the threat meter, which provides a good high-level overview of the analysis results (as shown below).

Here’s a summary of the resources available to help you make the most of the new features in XG Firewall v18, including the new zero-day threat protection capabilities:
If you’re new to Sophos XG Firewall, learn more about the great benefits and features XG Firewall can deliver to your network.
Net Universe offers all Sophos Devices and subscritpions also consultant services with worldwide Delivery Services.
Send us an email to [email protected] for more information or visit https://www.netuniversecorp.com/sophos.